Oct
2
Eircom’s Response to the Security Issues Recently Raised
Filed Under Computers & Tech, Security on October 2, 2007 at 1:48 am
Please note that this article is a follow-on article from two previous articles (Eircom Exposes Its Broadband Customers to Serious Security Risks and Eircom Security – More Bad News and Some Suggested Solutions). The previous articles lay out the problems and some suggested solutions in detail. This article will not repeat those detailed explanations and justifications. I am writing this article with the assumption that readers will have first read the two original articles.
This article starts by presenting the details of Eircom’s response before providing a brief analysis leading to some conclusions. For those of you too lazy to read the whole article, were this to be school I’d give Eircom a passing grade, but not a great one. Say a high D or a low C.
[tags]Eircom, Netopia, WEP, WPA[/tags]
The Response
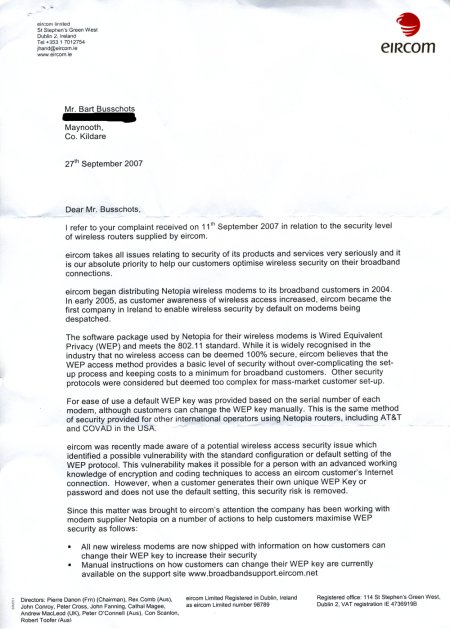
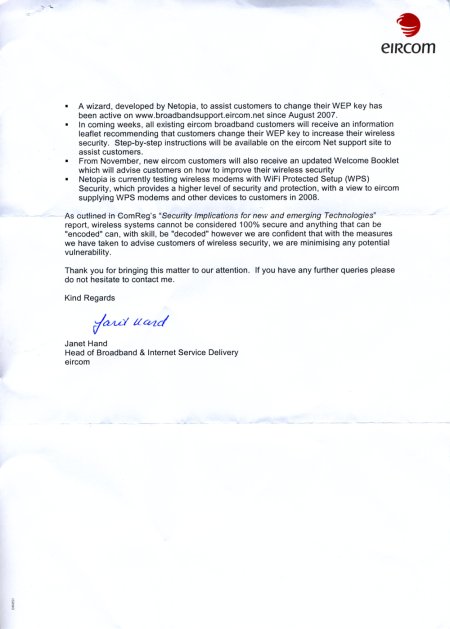
This article is based on the letter I received from Eircom today in response to the complaint I lodged with them on the 11th of September this year, and the content of their new Wireless security page. Since I’m too lazy to transcribe the reply from Eircom I scanned it in and have included the scans below. Eircom’s new wireless security page can be found at wirelesssecurity.eircom.net. Of particular interest is their new page with instructions to help users Enhance Wireless Security.
Analysis
In my previous articles I raised three problems: the flaw in the generation of the default keys and SSIDs, the use of WEP over WPA, and the lack of a password on the routers. I will look at each in turn.
The Flaw in the default WEP Keys and SSIDs
In summary, there are a number of programs (I’ve seen at least three, a C++ one, a Java one, and a web-based one using PHP) doing the rounds on the net which allow users to get the default WEP key for an Eircom Netopia router from it’s default SSID (name). This means that with a default configuration your network can be trivially entered by an attacker in possession of one of these programs. This problem can be fixed by changing either the SSID or the WEP key or both.
In response to this problem Eircom have issued an advisory on their web page and will be directly contacting their customers. The advisory provides a link to a page with instructions for changing your SSID and WEP key.
This, to me, is an adequate response. Realistically, I don’t see what else Eircom could have done. So, we’ll give them full marks on this one.
WEP rather than WPA
Again just a quick recap. The Netopia routers support two wireless encryption modes, WEP and WPA. WEP has been very badly compromised. WPA is not perfect, but, assuming users use a long random encryption key, WPA provides significantly increased security over WEP. Some older devices and operating systems don’t support WPA.
Despite the fact that the Netopia routers supplied by Eircom do support WPA neither Eircom’s old welcome booklet, old install CD, nor old website gave instructions for setting up WPA. In response to my complain Eircom have now updated the instructions on their site to include limited discussion of WPA. Eircom point out that WPA provides more security than WEP but don’t go into the shortcomings of WEP. Eircom will also be updating their welcome pack and their install CD.
This is an adequate response but not a great one. Eircom fell short of making WPA the default or even advising people to use WPA over WEP where possible. There are understandable reasons for this, but it’s still disappointing. I also noticed that Eircom did the smart thing and did some ‘ass-covering’ too:
It is the customers responsibility to ensure that they use a suitable level of security to meet their own individual requirements.
No Password on The Router
If users have set no password on their router it is possible to take it over simply by luring them to a malicious web page. These attacks reply solely on standard JavaScript and are not dependent on any bugs or vulnerabilities. These attacks have been reported in the wild but do not appear to be very common yet. I would guess that they will get more common as time goes on.
Eircom ignored this entire branch of my complaint and have done nothing to address the issue. A great big zero for this I’m afraid.
Some Good Advice Added
I was very pleased to see the following very sensible advice added to the ‘Enhance wireless security’ page on the Eircom site:
If you are not using wireless access, that is, if you are using an ethernet cable to connect your modem to your computer, eircom recommends that you disable the wireless feature on your modem completely.
Conclusions
First and foremost I’m glad to see that Eircom have responded to two of these three issues. The response is not perfect, but it is prompt (considering Eircom is a large corporation) and relatively comprehensive. One of my three issues was addressed as well as could be expected, another was addressed in a reasonable but slightly disappointing way, but the last was totally ignored. Being generous that’s two out of three, though I think one and a half out of three is probably fairer.
If you are an Eircom broadband user with a Netopia modem I would suggest you take the following steps to improve your security:
- Change you SSID (Update: This is not enough on it’s own, this only deters users of SOME of the key gen programs out there. You MUST change your key too)
- Switch to WPA with a strong randomly generated key (ideally the full 63 characters logn)
- Set a password on your router (and write it down so you remember it 🙂 )
Related Links
- Related thread on boards.ie – Eircom Netopia Routers Are Wide Open
- Related article on Silicon Republic – Security hole discovered in Eircom modems
- Update: For a much more detailed list of reltaed links see LoneWolf’s Blog – Eircom Quick Update







[…] In the words of a former roadie for Metallica: “New shit has come to light, man.” Bart got a reply from Eircom. I am surprised to say that it looks like everyone’s favourite Irish […]
Yeah, stories going round alright:
http://www.rte.ie/news/2007/1002/eircom.html
Indeed – nice one!
Congrats to Bart and all who worked on bringing this issue to light in the first place.
[…] two of them, with internal links as to where this all came from: BadWolf Zone » Eircom Quick Update Eircom’s Response to the Security Issues Recently Raised : Bart Busschots __________________ Counting down to: Two weeks in Melbourne! 15 days, 11 hours, 2 […]
More from BreakingNews.ie on this one:
http://www.breakingnews.ie/ireland/mhmhaueyeysn/
Hey Bart
Was reading Ray Foley’s Blog (Today Fm) and found this.
http://rayfoleyshow.blogspot.com/2007/10/eircom-wireless.html
I’ve just had a very VERY infuriating phone call with one of their technicians. Ahem.
This isn’t even the main part of the problem but can someone click the ‘here’ link on this page: http://home.eircom.net/html/change_wep_key.html and tell me what happens. It’s the link where it says: – Make sure the computer’s TCP/IP properties are set to obtain an IP address and DNS Server address automatically. Instructions on how to do this can be found here. ALl it does for me is bring up the same page I’m already on.
Also the other link they give on that page ie your computer IP address, doesn’t bring up the right information on my computer. It brings up a Netopia page alright, but it looks like an older version than the one on the guideline page, and it is missing a very vital link ie the 3D wireless link. Apparently, I don’t have the right software. When I asked what the right software is, I was told : Internet Explorer 7. I said I had tried this, AND Firefox and neither had worked. He told me, I had to use Internet Explorer 7. I reiterated that I was using Internet Explorer 7 and that also, their webpage says: ”If you do not already have the Netopia page displayed, open your browser (eg. Internet Explorer or Firefox).”
He then told me there was absolutely nothing they could do for me. I asked him could I speak to a supervisor, there wasn’t one there. So he gave me the complaints number which doesn’t open until tomorrow.
Hopefully they did record my call so I will have an exact record of what I was told.
”Also the other link they give on that page ie your computer IP address, doesn’t bring up the right information on my computer.”
Sorry, thought that was my computer address, but it’s actually the netopia one: 192.168.1.254
Hi Anne,
It sounds like you’ve had what I consider to be a typical Eircom experience, you appear to have been talking to someone who doesn’t have a clue. Obviously your problem was not covered by the help sheets this person had in front of them and since it appears they had no intelligence of their own they couldn’t help you.
The browser you use is quite irrelevant. The page in question is served out by your router and it’s missing a link it’s because the router is a different version that then one they show. It could be that it’s on older firmware or it could be that it is simply an older model. However, that shouldn’t matter, Eircom sold it to you so they should support it.
Expecting the link to magically show up by changing browser is nothing short of retarded in my view. It shows a total lack of any understanding of the technology by the “support” agent. I actually got so frustrated on the phone to Eircom once that I asked to speak to a competent person, the guy calmly told me that there was no one like that in there. I told him that was the first truthful thing he’d told me and slammed down the phone.
Also, don’t bother complaining. I tried it once. I got through to a guy with almost no English who seems to be paid to say “I understand” and bugger all more.
I’m afraid I can’t give you much help though, I don’t have one of these routers myself so I can’t really talk you through it. Good luck with Eircom. It may be worth simply calling back, you should get a different agent and with a lot of luck, maybe even a competent one!
Bart.
thanks for the GREAT post! Very useful…
Heh, I’m home visiting my parents and I came across this while looking for details on how to access the router. I asked Dad if he’d gotten a letter from Eircom and he said ‘oh yeah here it is, I left it for you to fix next time you were back’. I’d say there’s still a lot of people waiting for a visit from their tech savvy children before acting on it.
[…] letters which Eircom promised to send out to users to inform them of the security flaw I described previously have started arriving and one […]